Crypto
How To Protect Yourself With A More Secure Kind Of Multi-Factor Authentication
Published
2 years agoon

This is an opinion editorial by Heidi Porter, an entrepreneur with 35 years in technology.
User Security
In previous articles about security and data breaches, we discussed the need for multi-factor authentication (MFA) on your Bitcoin accounts and any other accounts you want to protect.
Hacks will continue to happen where your account is compromised or people are sent to a nefarious site and accidentally download malware instead of verified software.
This will be the first in a series of articles around more resilient user security for your accounts, nodes and apps. We’ll also cover better email options, better passwords and better use of a virtual private network (VPN).
The reality is that you’ll never be completely secure in any of your online financial transactions in any system. However, you can implement a more resilient toolset and best practices for stronger security.
What Is Multi-Factor Authentication And Why Do I Care?
According to the Cybersecurity and Infrastructure Security Agency, “Multi-factor authentication is a layered approach to securing data and applications where a system requires a user to present a combination of two or more credentials to verify a user’s identity for login.”
When we log into an online account, we’re often aiming to thwart an attacker or hacker using extra layers of verification — or locks.
Compared to your own home, multiple locks give more security. If one form of authentication is good, such as a password, then two forms (aka MFA) can be better.
Note that if you ONLY use biometric authentication, that is single-factor authentication. It’s just the biometric of whatever modality you’re using: thumb, iris, face recognition, etc. If you use 1 hardware key without a passphrase, that is also single-factor authentication.
However, if a biometric or key is used as a 2nd factor, it can meet the goal of multifactor authentication and be more secure than many app-based MFA.
With MFA, you must use at least 2 of these 3 authentication mechanisms:
- Something you know (password, PIN, etc)
- Something you have (code, device)
- Something you are (fingerprint or other biometric)
Where Should I Use MFA And What Kind Of MFA?
With MFA, you must have at least two authentication mechanisms.
If or when they eventually support MFA, at a minimum, you should have MFA set up for your:
- Bitcoin exchanges (but get your funds off them ASAP after buying).
- Bitcoin nodes and miners.
- Bitcoin and Lightning wallets.
- Lightning apps, such as RTL or Thunderhub.
- Cloud providers, such as Voltage accounts.
Note: Each account or application needs to support the type of MFA that you are using and you must register the MFA with the account or application.
MFA providers often include less secure options such as:
- SMS, Phone, or E-mail One-time passwords (OTPs) or Time-based One-Time Passwords (TOTP)
- Mobile push-based authentication (more secure if managed properly).
MFA providers sometimes also include more secure options such as:
- Authenticator apps.
- Biometric verification.
- Hardware keys.
- Smart cards.
Guess what type of MFA most legacy financial institutions use? It’s usually one of the less secure MFA options. That said, authenticator apps and hardware keys for MFA are not all created equal.
MFA And Marketing Misinformation
First, let’s talk about the marketing of MFA. If your MFA provider touts itself as unhackable or 99% unhackable, they are spouting multi-factor B.S. and you should find another provider. All MFA is hackable. The goal is to have a less hackable, more phishing resistant, more resilient MFA.
Registering a phone number leaves the MFA vulnerable to SIM-swapping. If your MFA does not have a good backup mechanism, then that MFA option is vulnerable to loss.
Some MFA is more hackable.
Some MFA is more trackable.
Some MFA is more or less able to be backed up.
Some MFA is more or less accessible in some environments.
Less Hackable and Trackable MFA
Multi-factor authentication is more securely accomplished with an authenticator app, smart card or hardware key, like a Yubikey.
So if you have an app-based or hardware MFA, you’re good, right? Well, no. Even if you are using app-based or hardware MFA, not all authenticator apps and hardware devices are created equal. Let’s look at some of the most popular authenticator apps and some of their vulnerabilities with tracking, hacking and backing up.
- Twilio Authy requires your phone number, which could open you up to compromise via SIM-card-swap. Initial setup is SMS. Note: How comfortable are you with Authy given the recent internal data breach at Twilio?
- Microsoft Authenticator doesn’t require a phone number, but can’t transfer to Android as it is backed up to iCloud.
- Google Authenticator also doesn’t require a phone number, but does not have online backup and is only able to transfer from one phone to another.
In addition, all of these apps are considered by some to be less resilient and open to phishing or man-in-the-middle (MITM) attacks.
How Your Accounts And Finances Can Be Compromised
“People should use phishing-resistant MFA whenever they can to protect valuable data and systems” – Roger A. Grimes, cybersecurity expert and author of “Hacking Multifactor Authentication”
Just like many financial and data companies, Bitcoin companies have been the target of multiple data breaches where attackers have obtained email addresses and phone numbers of customers.
Even without these breaches, it’s not especially hard to find someone’s email addresses and phone numbers (as mentioned in previous articles, best practice is to use a separate email and phone number for your Bitcoin accounts).
With these emails, attackers can perform phishing attacks and intercept the login credentials: both password and multi-factor authentication you have used as a second authentication factor for any of your accounts.
Let’s take a look at a typical MITM phishing attack process:
- You click a link (or scan a QR code) and you are sent to a site that looks very similar to the legitimate site you want to access.
- You type in your login credentials and then are prompted for your MFA code, which you type in.
- The attacker then captures the access session token for successful authentication to the legitimate site. You might even be directed to the valid site and never know that you have been hacked (note that the session token is usually only good for that one session).
- Attacker then has access to your account.
As an aside, be sure you have MFA attached to withdrawals on a wallet or exchange. Convenience is the enemy of security.
Phishing-Resistant MFA
To be resistant to phishing, your MFA should be an Authenticator Assurance Level 3 (AAL3) solution. AAL3 introduces several new requirements beyond AAL2, the most significant being the use of a hardware-based authenticator. There are several additional authentication characteristics that are required:
- Verifier impersonation resistance.
- Verifier compromise resistance.
- Authentication intent.
Fast Identity Online 2 (FIDO2) is an AAL3 solution. Going into the details about the different FIDO standards are beyond the scope of this article, but you can read a bit about it at “Your Complete Guide to FIDO, FIDO2 and WebAuthn.” Roger Grimes recommended the following AAL3-level MFA providers in March 2022 in his LinkedIn article “My List of Good Strong MFA.”
Important Note: Although I have not looked into all of these for my personal use, I believe any Bitcoin builder or Bitcoin company SHOULD ask their third-party providers or integration providers to provide details about what kind of MFA provider they use and ensure that it is phishing-resistant.
MFA Hardware Keys And Smart Cards
Hardware keys, like Yubikey, are less hackable forms of MFA. In addition, your phone number is not tied to the key, so it is less trackable. (I use Yubikey). Instead of a generated code that you enter, you press a button on your hardware key to authenticate. The hardware key has a unique code that is used to generate codes to confirm your identity as a second factor of authentication.
There are two caveats for hardware keys:
- Your app needs to support hardware keys.
- You can lose or damage your hardware key. Many services do allow you to configure more than one hardware key. If you lose the use of one, you can use the spare.
Smart cards are another form of MFA with similar phishing resistance. We won’t get into the details here as they seem to be less likely to be used for Bitcoin or Lightning-related MFA.
Mobile: Restricted Spaces Require Hardware Devices
Another consideration for multi-factor authentication is whether you would ever be in a situation where you need MFA and cannot use a cell phone or smartphone.
There are two big reasons this could happen for bitcoin users:
- Low or no cell coverage
- You don’t have or can’t use a smartphone
There can be other restrictions on cell phone use due to customer-facing work environments or personal preference. Call centers, K-12 schools or high-security environments like research and development labs are some areas where phones are restricted and you would therefore be unable to use your phone authenticator app.
In these special cases where you are using a computer and don’t have a smartphone, you would then need a smart card or hardware key for MFA. You would also need your application to support these hardware options.
Also, if you cannot use your cellphone at work, how are you supposed to stack sats in the restroom on your break?
Toward More Resilient MFA
MFA can be hacked and your accounts can be compromised. However, you can better protect yourself with more resilient and phishing-resistant MFA. You can also choose MFA that is not tied to your phone number and has an adequate back-up mechanism or ability to have a spare key.
Ongoing defense against cyber attacks is a continuing game of cat-and-mouse, or whack-a-mole. Your goal should be to become less hackable and less trackable.
Additional Resources:
- “Multi-Factor Authentication”
- “Digital Identity Guidelines”
- “Don’t Use Easily Phishable MFA and That’s Most MFA”
- “Hacks That Bypass Multi-Factor Authentication and How to Make Your MFA Solution Phishing Resistant”
- “Best practices for securing mobile-restricted environments with MFA”
This is a guest post by Heidi Porter. Opinions expressed are entirely their own and do not necessarily reflect those of BTC Inc. or Bitcoin Magazine.

Crypto
El Salvador Takes First Step To Issue Bitcoin Volcano Bonds
Published
2 years agoon
November 22, 2022
El Salvador’s Minister of the Economy Maria Luisa Hayem Brevé submitted a digital assets issuance bill to the country’s legislative assembly, paving the way for the launch of its bitcoin-backed “volcano” bonds.
First announced one year ago today, the pioneering initiative seeks to attract capital and investors to El Salvador. It was revealed at the time the plans to issue $1 billion in bonds on the Liquid Network, a federated Bitcoin sidechain, with the proceedings of the bonds being split between a $500 million direct allocation to bitcoin and an investment of the same amount in building out energy and bitcoin mining infrastructure in the region.
A sidechain is an independent blockchain that runs parallel to another blockchain, allowing for tokens from that blockchain to be used securely in the sidechain while abiding by a different set of rules, performance requirements, and security mechanisms. Liquid is a sidechain of Bitcoin that allows bitcoin to flow between the Liquid and Bitcoin networks with a two-way peg. A representation of bitcoin used in the Liquid network is referred to as L-BTC. Its verifiably equivalent amount of BTC is managed and secured by the network’s members, called functionaries.
“Digital securities law will enable El Salvador to be the financial center of central and south America,” wrote Paolo Ardoino, CTO of cryptocurrency exchange Bitfinex, on Twitter.
Bitfinex is set to be granted a license in order to be able to process and list the bond issuance in El Salvador.
The bonds will pay a 6.5% yield and enable fast-tracked citizenship for investors. The government will share half the additional gains with investors as a Bitcoin Dividend once the original $500 million has been monetized. These dividends will be dispersed annually using Blockstream’s asset management platform.
The act of submitting the bill, which was hinted at earlier this year, kickstarts the first major milestone before the bonds can see the light of day. The next is getting it approved, which is expected to happen before Christmas, a source close to President Nayib Bukele told Bitcoin Magazine. The bill was submitted on November 17 and presented to the country’s Congress today. It is embedded in full below.
Crypto
How I’ll Talk To Family Members About Bitcoin This Thanksgiving
Published
2 years agoon
November 22, 2022
This is an opinion editorial by Joakim Book, a Research Fellow at the American Institute for Economic Research, contributor and copy editor for Bitcoin Magazine and a writer on all things money and financial history.
I don’t.
That’s it. That’s the article.
In all sincerity, that is the full message: Just don’t do it. It’s not worth it.
You’re not an excited teenager anymore, in desperate need of bragging credits or trying out your newfound wisdom. You’re not a preaching priestess with lost souls to save right before some imminent arrival of the day of reckoning. We have time.
Instead: just leave people alone. Seriously. They came to Thanksgiving dinner to relax and rejoice with family, laugh, tell stories and zone out for a day — not to be ambushed with what to them will sound like a deranged rant in some obscure topic they couldn’t care less about. Even if it’s the monetary system, which nobody understands anyway.
Get real.
If you’re not convinced of this Dale Carnegie-esque social approach, and you still naively think that your meager words in between bites can change anybody’s view on anything, here are some more serious reasons for why you don’t talk to friends and family about Bitcoin the protocol — but most certainly not bitcoin, the asset:
- Your family and friends don’t want to hear it. Move on.
- For op-sec reasons, you don’t want to draw unnecessary attention to the fact that you probably have a decent bitcoin stack. Hopefully, family and close friends should be safe enough to confide in, but people talk and that gossip can only hurt you.
- People find bitcoin interesting only when they’re ready to; everyone gets the price they deserve. Like Gigi says in “21 Lessons:”
“Bitcoin will be understood by you as soon as you are ready, and I also believe that the first fractions of a bitcoin will find you as soon as you are ready to receive them. In essence, everyone will get ₿itcoin at exactly the right time.”
It’s highly unlikely that your uncle or mother-in-law just happens to be at that stage, just when you’re about to sit down for dinner.
- Unless you can claim youth, old age or extreme poverty, there are very few people who genuinely haven’t heard of bitcoin. That means your evangelizing wouldn’t be preaching to lost, ignorant souls ready to be saved but the tired, huddled and jaded masses who could care less about the discovery that will change their societies more than the internal combustion engine, internet and Big Government combined. Big deal.
- What is the case, however, is that everyone in your prospective audience has already had a couple of touchpoints and rejected bitcoin for this or that standard FUD. It’s a scam; seems weird; it’s dead; let’s trust the central bankers, who have our best interest at heart.
No amount of FUD busting changes that impression, because nobody holds uninformed and fringe convictions for rational reasons, reasons that can be flipped by your enthusiastic arguments in-between wiping off cranberry sauce and grabbing another turkey slice. - It really is bad form to talk about money — and bitcoin is the best money there is. Be classy.
Now, I’m not saying to never ever talk about Bitcoin. We love to talk Bitcoin — that’s why we go to meetups, join Twitter Spaces, write, code, run nodes, listen to podcasts, attend conferences. People there get something about this monetary rebellion and have opted in to be part of it. Your unsuspecting family members have not; ambushing them with the wonders of multisig, the magically fast Lightning transactions or how they too really need to get on this hype train, like, yesterday, is unlikely to go down well.
However, if in the post-dinner lull on the porch someone comes to you one-on-one, whisky in hand and of an inquisitive mind, that’s a very different story. That’s personal rather than public, and it’s without the time constraints that so usually trouble us. It involves clarifying questions or doubts for somebody who is both expressively curious about the topic and available for the talk. That’s rare — cherish it, and nurture it.
Last year I wrote something about the proper role of political conversations in social settings. Since November was also election month, it’s appropriate to cite here:
“Politics, I’m starting to believe, best belongs in the closet — rebranded and brought out for the specific occasion. Or perhaps the bedroom, with those you most trust, love, and respect. Not in public, not with strangers, not with friends, and most certainly not with other people in your community. Purge it from your being as much as you possibly could, and refuse to let political issues invade the areas of our lives that we cherish; politics and political disagreements don’t belong there, and our lives are too important to let them be ruled by (mostly contrived) political disagreements.”
If anything, those words seem more true today than they even did then. And I posit to you that the same applies for bitcoin.
Everyone has some sort of impression or opinion of bitcoin — and most of them are plain wrong. But there’s nothing people love more than a savior in white armor, riding in to dispel their errors about some thing they are freshly out of fucks for. Just like politics, nobody really cares.
Leave them alone. They will find bitcoin in their own time, just like all of us did.
This is a guest post by Joakim Book. Opinions expressed are entirely their own and do not necessarily reflect those of BTC Inc or Bitcoin Magazine.

This is an opinion editorial by Federico Tenga, a long time contributor to Bitcoin projects with experience as start-up founder, consultant and educator.
The term “smart contracts” predates the invention of the blockchain and Bitcoin itself. Its first mention is in a 1994 article by Nick Szabo, who defined smart contracts as a “computerized transaction protocol that executes the terms of a contract.” While by this definition Bitcoin, thanks to its scripting language, supported smart contracts from the very first block, the term was popularized only later by Ethereum promoters, who twisted the original definition as “code that is redundantly executed by all nodes in a global consensus network”
While delegating code execution to a global consensus network has advantages (e.g. it is easy to deploy unowed contracts, such as the popularly automated market makers), this design has one major flaw: lack of scalability (and privacy). If every node in a network must redundantly run the same code, the amount of code that can actually be executed without excessively increasing the cost of running a node (and thus preserving decentralization) remains scarce, meaning that only a small number of contracts can be executed.
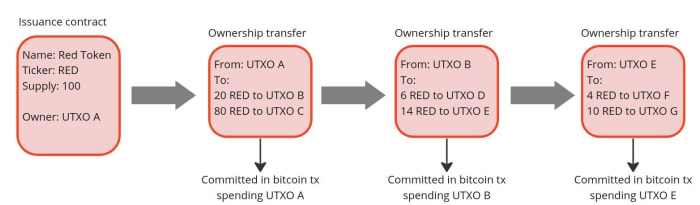
But what if we could design a system where the terms of the contract are executed and validated only by the parties involved, rather than by all members of the network? Let us imagine the example of a company that wants to issue shares. Instead of publishing the issuance contract publicly on a global ledger and using that ledger to track all future transfers of ownership, it could simply issue the shares privately and pass to the buyers the right to further transfer them. Then, the right to transfer ownership can be passed on to each new owner as if it were an amendment to the original issuance contract. In this way, each owner can independently verify that the shares he or she received are genuine by reading the original contract and validating that all the history of amendments that moved the shares conform to the rules set forth in the original contract.
This is actually nothing new, it is indeed the same mechanism that was used to transfer property before public registers became popular. In the U.K., for example, it was not compulsory to register a property when its ownership was transferred until the ‘90s. This means that still today over 15% of land in England and Wales is unregistered. If you are buying an unregistered property, instead of checking on a registry if the seller is the true owner, you would have to verify an unbroken chain of ownership going back at least 15 years (a period considered long enough to assume that the seller has sufficient title to the property). In doing so, you must ensure that any transfer of ownership has been carried out correctly and that any mortgages used for previous transactions have been paid off in full. This model has the advantage of improved privacy over ownership, and you do not have to rely on the maintainer of the public land register. On the other hand, it makes the verification of the seller’s ownership much more complicated for the buyer.

Source: Title deed of unregistered real estate propriety
How can the transfer of unregistered properties be improved? First of all, by making it a digitized process. If there is code that can be run by a computer to verify that all the history of ownership transfers is in compliance with the original contract rules, buying and selling becomes much faster and cheaper.
Secondly, to avoid the risk of the seller double-spending their asset, a system of proof of publication must be implemented. For example, we could implement a rule that every transfer of ownership must be committed on a predefined spot of a well-known newspaper (e.g. put the hash of the transfer of ownership in the upper-right corner of the first page of the New York Times). Since you cannot place the hash of a transfer in the same place twice, this prevents double-spending attempts. However, using a famous newspaper for this purpose has some disadvantages:
- You have to buy a lot of newspapers for the verification process. Not very practical.
- Each contract needs its own space in the newspaper. Not very scalable.
- The newspaper editor can easily censor or, even worse, simulate double-spending by putting a random hash in your slot, making any potential buyer of your asset think it has been sold before, and discouraging them from buying it. Not very trustless.
For these reasons, a better place to post proof of ownership transfers needs to be found. And what better option than the Bitcoin blockchain, an already established trusted public ledger with strong incentives to keep it censorship-resistant and decentralized?
If we use Bitcoin, we should not specify a fixed place in the block where the commitment to transfer ownership must occur (e.g. in the first transaction) because, just like with the editor of the New York Times, the miner could mess with it. A better approach is to place the commitment in a predefined Bitcoin transaction, more specifically in a transaction that originates from an unspent transaction output (UTXO) to which the ownership of the asset to be issued is linked. The link between an asset and a bitcoin UTXO can occur either in the contract that issues the asset or in a subsequent transfer of ownership, each time making the target UTXO the controller of the transferred asset. In this way, we have clearly defined where the obligation to transfer ownership should be (i.e in the Bitcoin transaction originating from a particular UTXO). Anyone running a Bitcoin node can independently verify the commitments and neither the miners nor any other entity are able to censor or interfere with the asset transfer in any way.
Since on the Bitcoin blockchain we only publish a commitment of an ownership transfer, not the content of the transfer itself, the seller needs a dedicated communication channel to provide the buyer with all the proofs that the ownership transfer is valid. This could be done in a number of ways, potentially even by printing out the proofs and shipping them with a carrier pigeon, which, while a bit impractical, would still do the job. But the best option to avoid the censorship and privacy violations is establish a direct peer-to-peer encrypted communication, which compared to the pigeons also has the advantage of being easy to integrate with a software to verify the proofs received from the counterparty.
This model just described for client-side validated contracts and ownership transfers is exactly what has been implemented with the RGB protocol. With RGB, it is possible to create a contract that defines rights, assigns them to one or more existing bitcoin UTXO and specifies how their ownership can be transferred. The contract can be created starting from a template, called a “schema,” in which the creator of the contract only adjusts the parameters and ownership rights, as is done with traditional legal contracts. Currently, there are two types of schemas in RGB: one for issuing fungible tokens (RGB20) and a second for issuing collectibles (RGB21), but in the future, more schemas can be developed by anyone in a permissionless fashion without requiring changes at the protocol level.
To use a more practical example, an issuer of fungible assets (e.g. company shares, stablecoins, etc.) can use the RGB20 schema template and create a contract defining how many tokens it will issue, the name of the asset and some additional metadata associated with it. It can then define which bitcoin UTXO has the right to transfer ownership of the created tokens and assign other rights to other UTXOs, such as the right to make a secondary issuance or to renominate the asset. Each client receiving tokens created by this contract will be able to verify the content of the Genesis contract and validate that any transfer of ownership in the history of the token received has complied with the rules set out therein.
So what can we do with RGB in practice today? First and foremost, it enables the issuance and the transfer of tokenized assets with better scalability and privacy compared to any existing alternative. On the privacy side, RGB benefits from the fact that all transfer-related data is kept client-side, so a blockchain observer cannot extract any information about the user’s financial activities (it is not even possible to distinguish a bitcoin transaction containing an RGB commitment from a regular one), moreover, the receiver shares with the sender only blinded UTXO (i. e. the hash of the concatenation between the UTXO in which she wish to receive the assets and a random number) instead of the UTXO itself, so it is not possible for the payer to monitor future activities of the receiver. To further increase the privacy of users, RGB also adopts the bulletproof cryptographic mechanism to hide the amounts in the history of asset transfers, so that even future owners of assets have an obfuscated view of the financial behavior of previous holders.
In terms of scalability, RGB offers some advantages as well. First of all, most of the data is kept off-chain, as the blockchain is only used as a commitment layer, reducing the fees that need to be paid and meaning that each client only validates the transfers it is interested in instead of all the activity of a global network. Since an RGB transfer still requires a Bitcoin transaction, the fee saving may seem minimal, but when you start introducing transaction batching they can quickly become massive. Indeed, it is possible to transfer all the tokens (or, more generally, “rights”) associated with a UTXO towards an arbitrary amount of recipients with a single commitment in a single bitcoin transaction. Let’s assume you are a service provider making payouts to several users at once. With RGB, you can commit in a single Bitcoin transaction thousands of transfers to thousands of users requesting different types of assets, making the marginal cost of each single payout absolutely negligible.
Another fee-saving mechanism for issuers of low value assets is that in RGB the issuance of an asset does not require paying fees. This happens because the creation of an issuance contract does not need to be committed on the blockchain. A contract simply defines to which already existing UTXO the newly issued assets will be allocated to. So if you are an artist interested in creating collectible tokens, you can issue as many as you want for free and then only pay the bitcoin transaction fee when a buyer shows up and requests the token to be assigned to their UTXO.
Furthermore, because RGB is built on top of bitcoin transactions, it is also compatible with the Lightning Network. While it is not yet implemented at the time of writing, it will be possible to create asset-specific Lightning channels and route payments through them, similar to how it works with normal Lightning transactions.
Conclusion
RGB is a groundbreaking innovation that opens up to new use cases using a completely new paradigm, but which tools are available to use it? If you want to experiment with the core of the technology itself, you should directly try out the RGB node. If you want to build applications on top of RGB without having to deep dive into the complexity of the protocol, you can use the rgb-lib library, which provides a simple interface for developers. If you just want to try to issue and transfer assets, you can play with Iris Wallet for Android, whose code is also open source on GitHub. If you just want to learn more about RGB you can check out this list of resources.
This is a guest post by Federico Tenga. Opinions expressed are entirely their own and do not necessarily reflect those of BTC Inc or Bitcoin Magazine.